TL;DR
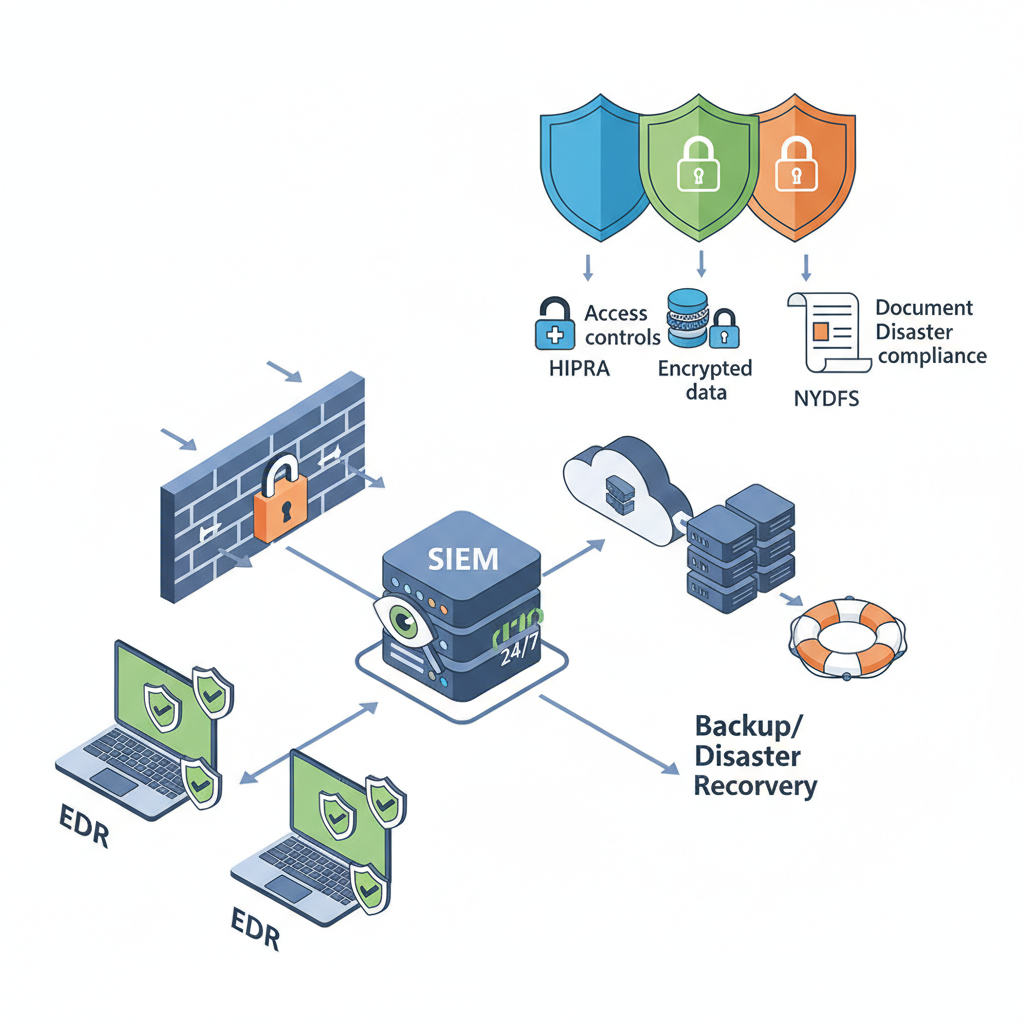
- Regulated businesses need MSPs that deliver EDR, 24/7 SIEM, enterprise backup, and documented compliance artifacts.
- Quick action: request SOC 2 or equivalent reports and a written BAA for HIPAA-covered entities; require evidence of NY DFS alignment (23 NYCRR 500) and written record-retention practices for FINRA-regulated firms.

Introduction — why regulated businesses need specialized MSPs
If your company handles protected health information, broker-dealer records, or operates under New York’s financial rules, a routine help-desk MSP won’t cut it. You face fines, mandatory disclosure timelines, and contractual penalties when a breach exposes regulated data. The immediate problem is twofold: you must defend against modern threats, and you must prove controls to auditors and regulators.
Quick answer: choose a managed IT and security partner that provides enterprise-grade endpoint protection, 24/7 detection with retained logs, tested backups and ransomware recovery, and written compliance artifacts (SOC 2, BAAs, policies). Request the MSP's SOC 2 or equivalent report and a written BAA for HIPAA-covered entities. For more on this, see Choosing managed it services.
Definitions for quick reference: HIPAA protects health information and mandates safeguards for electronic protected health information; FINRA enforces broker-dealer obligations including record retention and secure communications; NY DFS (23 NYCRR 500) requires financial institutions to maintain a cybersecurity program, incident reporting, and third-party risk management. Typical MSP responsibilities include monitoring, patching, logging, and incident response support; client responsibilities typically include policy ownership, privileged account oversight, and contractual notice obligations. For more on this, see It cybersecurity solutions.
Who this is NOT for:
- Companies without regulated data who only need basic break/fix IT support.
- Firms that cannot commit an internal owner for compliance tasks (policy sign-off, vendor governance).
- Organizations that refuse to allow centralized logging or managed backups for regulatory evidence.
Core Security Capabilities to Require
Without specific technical controls, regulated firms fail audits even if they’ve never been breached. Insist the MSP delivers these core capabilities and measurable artifacts: endpoint detection and response (EDR) with automated containment, a 24/7 SIEM with retained logs for at least 1 year, immutable off-site backups with routine recovery tests, multifactor authentication for all administrative access, and documented incident response playbooks.
Concrete thresholds and artifacts you should demand: EDR telemetry retention for a minimum of 90 days, SIEM log retention of 365 days for critical systems, quarterly patch compliance >95% on critical CVEs, and annual tabletop exercises documented in the incident log. A managed security checklist for small business should include these exact items to be audit-ready.
Require measurable retention windows: 90 days for endpoint telemetry and 365 days for SIEM logs on regulated systems.
Validated recovery beats theoretical backups—schedule and document full restores at least twice per year.
Endpoint Detection & Response (EDR)
EDR is the last line before ransomware or data exfiltration completes. For regulated businesses, EDR must provide continuous behavioral detection, automated containment (isolate host), and forensic data export. Ask for examples of threat-hunt reports, the types of telemetry collected (process, network, file), and whether the vendor supports on-demand forensic snapshots.
Practical thresholds: require P95 detection-to-containment under 30 minutes for critical events, and daily health checks showing 100% coverage on endpoints. For HIPAA scenarios, confirm EDR supports encrypted disk for mobile devices and logs access attempts to ePHI.
24/7 SIEM & Managed Detection
A SIEM used by regulated firms must do more than generate alerts. It needs tuned rules for your sector, retained immutable logs, and a staffed SOC for 24/7 triage. Verify the MSP’s incident escalation matrix and average analyst response time. Also confirm that raw logs are exportable for regulator requests.
Example requirement: a SIEM that keeps raw logs for 12 months, stores integrity hashes, and provides monthly summary reports plus immediate notification within mandated reporting windows. For NY DFS compliance, those reporting windows and evidence of notification workflows matter—document them in the incident playbook.
Backup, Disaster Recovery, and Ransomware Protections
Backups must be immutable, isolated, and tested. Ask for the backup retention policy, frequency, and last successful restore test date. A managed backup strategy for regulated data typically includes daily incremental backups, weekly fulls, and at least 90 days of retention for active datasets, with at least one off-site encrypted copy for regulatory e-discovery.
Concrete artifact: a restore test report showing a successful full system restore within an agreed Recovery Time Objective (RTO). For financial and healthcare firms, insist on proof of air-gapped or immutable snapshots to prevent encryption by ransomware.
Compliance-Specific Requirements
Each regulator has distinct evidence expectations. Your MSP should map technical controls to requirements and produce artifacts auditors accept: policy documents, system configuration snapshots, log exports, and proof of testing. Below are specifics for HIPAA, FINRA, and NY DFS with examples you can request.
HIPAA — logging, BAAs, encryption, access controls
HIPAA requires administrative, physical, and technical safeguards for ePHI. From an MSP, request a written Business Associate Agreement (BAA) and evidence of encryption at rest and in transit for systems hosting ePHI. Ask for access control reports showing role-based access and MFA on all accounts that access PHI.
Quotable fact: "Request the MSP's SOC 2 or equivalent report and a written BAA for HIPAA-covered entities." Also request risk analysis documentation per HHS guidance (HHS Security Rule) and retention of audit logs for at least 6 years when required contractually or by state law.
FINRA — record retention, secure communications, audit logs
FINRA requires broker-dealers to retain communications and transaction records and to supervise electronic communications. For FINRA compliance, require archived secure communications (email, chat), immutable message logs, and proof of record retention policies tied to retention schedules. Ask the MSP how they handle e-discovery exports and chain-of-custody for audit evidence.
Search for concrete guarantees: retention exports in vendor-neutral formats, export within 48 hours for audit requests, and documented access controls for stored records. Use the phrase finra it requirements msp when mapping technical features to your compliance matrix.
NY DFS — incident reporting, tabletop exercises, third-party risk management
NY DFS (23 NYCRR 500) requires financial institutions to maintain a cybersecurity program, appoint personnel, perform risk assessments, run tabletop exercises, and report incidents promptly. Ask your MSP for evidence of tabletop exercise schedules, incident reporting templates, and third-party risk assessments for critical vendors.
Quotable fact: "Reference NY DFS Cybersecurity Regulation (23 NYCRR 500) for incident reporting and third-party risk controls." Confirm the MSP documents breach notification workflows that align with NJ/NY regional expectations for breach reporting and local counsel involvement.
Vendor Questions & Documentation Checklist (policies, audit reports, SOC 2)
When you evaluate an MSP, use a reproducible checklist. Below is a two-column comparison table you can copy for vendor scoring.
| Artifact | What to request |
|---|---|
| SOC 2 / audit report | Copy of latest report or bridge letter and scope of systems covered |
| BAA | Signed BAA for HIPAA-covered services |
| Incident playbook | Escalation matrix, reporting timelines, sample incident report |
| Backup test report | Last three full restores and dates |
| Third-party risk | Vendor inventory and risk ratings for sub-processors |
How to Validate an MSP’s Compliance Claims (evidence, third-party audits)
Claims mean nothing without evidence. Validate by reviewing third-party audit reports (SOC 2 Type II preferred), requesting sample logs and redacted incident reports, and confirming contract language for liability and notification. Ask for a list of sub-processors and their attestations. Verify technical claims by asking for configuration snapshots or screenshots of monitoring dashboards.
Decision rule: if the MSP cannot provide a current third-party audit covering the services you rely on, mark them as higher risk and require compensating controls. For HIPAA, confirm a signed BAA appears in the contract. For NY DFS, ask how the MSP supports incident reporting within required timeframes.
Implementation Roadmap & Local Support Considerations for NJ/NY
Start with a 30-day discovery: asset inventory, risk mapping, and quick remediations (patching and MFA). Months 2–3 focus on deploying EDR, centralizing logs into the SIEM, and enabling backups. Months 4–6 test restores, run a tabletop exercise, and finalize policies. Local considerations: choose an MSP with regional knowledge of NJ/NY breach laws and access to local counsel for regulated notifications.
| Phase | Deliverables (examples) |
|---|---|
| 30 days | Asset inventory, risk map, immediate patching list |
| 60–90 days | EDR rollout, SIEM onboarding, backup configuration |
| 90–180 days | Restore tests, tabletop, policy sign-offs |
Conclusion — sample checklist and call to action for a free security assessment
Sample checklist (copyable):
- Obtain SOC 2 or equivalent audit report from MSP.
- Get a signed BAA for HIPAA-covered services.
- Confirm EDR coverage and SIEM retention (90/365 days).
- Verify immutable backups and at least two documented restore tests per year.
- Request incident playbook and recent tabletop exercise report.
If you operate in New Jersey or New York, prioritize an MSP that understands regional reporting rules and can provide the artifacts auditors expect. For specific offerings, review our services or request a demonstration via our services. To schedule a free security assessment or get answers about HIPAA MSP checklists, FINRA requirements, or NY DFS cybersecurity compliance, contact us, visit contact us, or use contact us to reach the team.
References
- The Security Rule | HHS.gov
- Guidance on Risk Analysis Requirements | HHS
- SP 800-66 Rev. 2 | NIST
- Cybersecurity Resource Center | NY DFS
- CIS Critical Security Controls v8.1
FAQ
What is managed it security checklist for regulated businesses in new jersey & new york (hipaa, finra, ny dfs)?
A managed it security checklist for regulated businesses is a sector-specific set of technical controls and documentation that an MSP must deliver—EDR, SIEM, immutable backups, incident playbooks, SOC 2 reports, and BAAs where applicable—to meet HIPAA, FINRA, and NY DFS requirements.
How does managed it security checklist for regulated businesses in new jersey & new york (hipaa, finra, ny dfs) work?
The checklist maps regulator obligations to operational controls: deploy EDR and SIEM for detection, enforce encryption and MFA for access, run tested backups for recovery, and collect audit artifacts (logs, reports, BAAs) to prove compliance during audits or incident investigations.

